1. The Quiet Strength of the Swiss E‑ID
Digital identity can feel intimidating. Many imagine a giant government database tracking every login or storing every detail of their life. Others worry about what happens if their phone is stolen.
The truth is much simpler — and much safer.
The Swiss E‑ID is designed so that you stay in control, your identity stays on your device, and even in the worst case, a thief cannot “take over your life.”
2. Your E‑ID Lives on Your Device — Not in a Government Database
When you receive an E‑ID, the government does not store it anywhere. Your E‑ID is stored only on:
- your phone’s Secure Enclave (iPhone)
- Android StrongBox
- a certified hardware token
These chips protect sensitive data. This means:
- No central database to hack, leak, or misuse
- Even if your device is stolen, the E‑ID cannot be extracted or copied
3. How the E‑ID Is Created — Without Storing Anything Centrally
Step 1 — You prove who you are with a passport or official ID.
Step 2 — The issuer creates a digital signature for your verified attributes.
Step 3 — The signed E‑ID is delivered securely to your device.
Step 4 — The issuer does not retain a copy; they only publish a public key for verification.
No central storage. No tracking. No database of citizens.
4. What Cryptography Means — In Plain Language
Cryptography is math that protects secrets:
- The issuer signs your E‑ID with a private key.
- Anyone can verify the signature using the issuer’s public key.
- The signature cannot be forged, copied, or altered.
This same principle protects online banking, HTTPS websites, and digital payments.
5. What Happens If Your Phone Is Stolen
Even if someone steals your phone, they cannot:
- Extract your E‑ID
- Copy it to another device
- Read your personal data
- Impersonate you after revocation
Temporary use is only possible if they unlock your phone and pass biometrics. Even then:
- Only low-value logins are possible
- Banks or government portals remain protected
- Cloning or continued use is impossible after revocation
6. Revocation Is Your Kill Switch
If your phone is lost:
- Report it to the issuer
- The old E‑ID is marked revoked
- Every verifier automatically rejects it
- You receive a new E‑ID on your device
The new cryptographic reference is tied to a fresh key pair. Services continue working without any updates on your part.
Why Your New E‑ID Works Seamlessly
- The new E-ID generates a completely new cryptographic key pair.
- The issuer signs your verified attributes again.
- Verification systems check for a valid, non-revoked credential, not the old reference.
- The old credential remains revoked; the new one is immediately usable.
Revocation doesn’t replace your identity — it rotates the cryptographic handle that represents it.
7. Recovery Without the Original E-ID
Even if your E-ID is gone, you can revoke or replace it via separate recovery channels:
- In-person verification at canton/post/issuer
- Video identification with certified officials
- Pre-registered recovery tokens or bank login
These channels prove your personhood, not the lost E-ID. The issuer then updates the revocation registry and optionally issues a new credential. The E-ID device itself is never needed to trigger revocation.
Think of it like replacing a lost passport: the office trusts other identity evidence to issue a new one while immediately invalidating the old one.
8. Privacy and Traceability
Yes — in theory, tracing an individual through revocation, recovery, or E-ID usage is conceivable. In practice, this is extremely difficult and practically impossible under the current swiyu design (January 2026, with the public beta live and a productive rollout approaching summer 2026).
The system prioritizes privacy-by-design, drawing from self-sovereign identity principles and using the Token Status List (TSL) for revocation.
Why tracing is technically difficult:
- Bulk/aggregated TSL checks — verifiers download lists covering millions of credentials; no individual lookups occur.
- Decoupled recovery from usage — recovery proves personhood only, without sending the old credential’s ID or history.
- No central tracking — the Base Registry holds only public keys/aggregated revocation info; no logs tie queries to individuals.
- Selective disclosure + unlinkable proofs — everyday verification reveals only what you explicitly reveal, making correlation extremely difficult.
Extreme scenarios: Even with sophisticated cross-correlation attacks or mass data requests, tracing an individual would require enormous technical effort, cooperation from multiple private parties, and is still probabilistic. Swiss law further prohibits routine surveillance, making tracking legally forbidden.
Takeaway: “Swiss swiyu makes individual tracking technically impractical and legally prohibited — privacy isn’t absolute, but it is robust enough for real-world use.”
9. Why This Fits Swiss Values
- E-ID is device-bound, not centrally stored
- Revocation and recovery are secure, privacy-preserving, and seamless
- Verification works across services without exposing personal data
- Users maintain full control over their digital identity
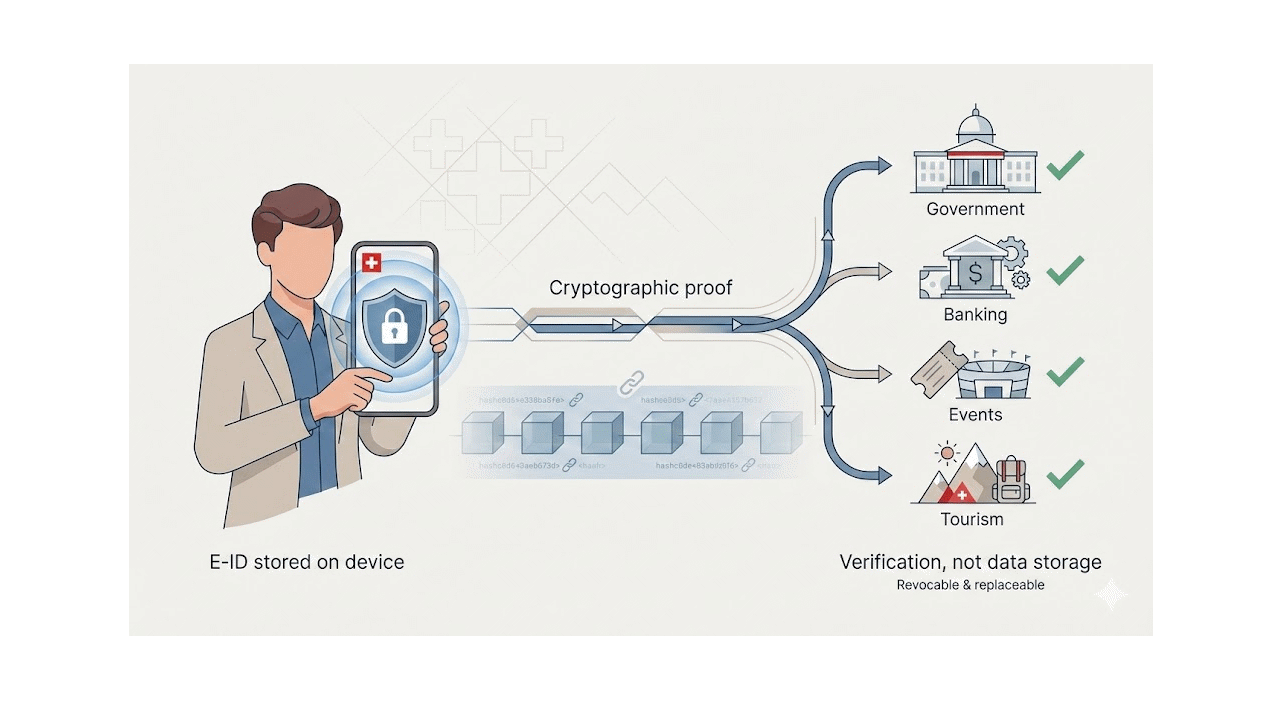
10. Practical Uses of Your Swiss E‑ID
Beyond secure login, Swiss E‑ID enables real-world applications across multiple sectors, often leveraging blockchain or verifiable credentials for tamper-evident records:
- Events and ticketing: prove age, membership, or eligibility without issuing paper tickets or sharing extra personal data.
- Government services: submit applications, access permits, or verify documents digitally, with blockchain ensuring authenticity and auditability.
- Banking and finance: open accounts, approve transactions, or sign agreements with cryptographic proofs instead of repeated KYC checks.
- Tourism and hospitality: confirm identity or residency for bookings, transport, or attractions without handing over passports.
In all cases, your E-ID proves who you are, without storing your personal data on each service, and blockchain or similar verifiable infrastructure provides a secure, tamper-evident audit trail. This makes transactions faster, more reliable, and privacy-preserving.
11. In Short
A modern Swiss E-ID is:
- Stored only on your device
- Never centrally stored
- Protected by strong cryptography
- Revocable safely
- Usable immediately after reissue
- Fully privacy-preserving under swiyu design
It’s a digital passport in your pocket, not a government database.
12. Closing
Your E-ID is a secure, convenient way to prove your identity, but control and privacy remain with you. Losing a device doesn’t lock you out or expose your identity. Swiss design ensures revocation, recovery, and everyday usage are safe, private, and practical.
At Parowls Software GmbH, we help Swiss organisations navigate secure digital identity, blockchain integration, and practical workflow implementation. If you want guidance on deploying E-ID solutions, cryptographic verification, or privacy-preserving digital workflows, contact us to discuss how we can make these technologies work seamlessly in your environment.